Legacy “collect and correlate” SIEMs are not equipped to handle today’s complex, data-intensive, dynamic environments. Are you drowning in irrelevant alerts and unjustifiable data ingestion bills? If your SIEM is letting you down, Gurucul can help.
Transform and empower your SOC with the converged capabilities of SIEM, UEBA, SOAR and Identity & Access Analytics from the industry’s most comprehensive and flexible Next-Gen SIEM.
Empower Your SOC with Unified Security Analytics
Give your analysts radical clarity of your threat landscape from a single interface, designed to deliver value day one. Real-time, prioritized and actionable insights means less time chasing alerts and more time reducing dwell time by quickly eradicating threats.
Reap the cost and scale benefits of any security data lake you choose and start rebalancing the out-of-control data costs inherit to traditional SIEMs. You can leverage Gurucul’s Hadoop data lake or bring you own, as well as enjoy the flexibility to build a centralized or decentralized SIEM architecture. The ability to run federated search across any data store, regardless of location or vendor, gives you ultimate control of your data architecture without the cost of data duplication or transfer.
To discern true threats quickly you must have the right context. Gurucul’s Next-Gen SIEM easily ingests analyzes and searches any security and non-security data, providing you with complete visibility and context to detect, investigate and manage threats across your entire IT estate.
Gurucul’s ML-powered data fabric rapidly ingests, normalizes, enriches, filters and forwards any data source . You don’t need a third-party data streaming tool or wait unacceptable lengths for expensive vendor integration delivery. Hundreds of data enrichment techniques are available in our wizard-driven UI and a 2 day SLA for new integrations means your analytic models are always being fed the right data.
Go from ingestion to high-fidelity detections in seconds with over 10,000 pieces of pre-built detection models and threat content. Enabled out-of-the-box, but everything is fully customizable. From dashboards to ML models and risk scoring, you can tailor Gurucul’s Next-Gen SIEM to you exact requirements.
Improve detection coverage with 3,000+ Machine Learning models that automatically apply a wide breadth of behavioral analytics to data from any source. It analyzes endpoint, network application, cloud, IoT, identity, network, structured and unstructured data, and even unknown data sources.
A single, consolidated risk score is generated for any user, entity, application or asset group across every transaction and entitlement. Prioritize risk with normalized 0-100 scoring and take action with a library of response playbooks. Risk scoring and playbooks can be customized to manage risk tolerance and response specific to your business.
Alleviate your SOC analysts from cumbersome investigations and give them an AI assistant to help streamline investigations and hunting. Now your analysts can spend more time responding to true threats and conducting focused hunting exercises with capabilities once reserved for data scientists.
Explore the Full Security Analytics Platform
Gurucul’s Next-Gen SIEM is one product capability of our Dynamic Security Analytics Platform. We invite you learn more about our unique design pillars that allow us to deliver radical clarity into your cyber risk.
If SIEM Rip and Replace Feels Overwhelming
Rebalance the duties of your existing SIEM back to log management basics and leave the rest to Gurucul.
Take a Guided Next-Gen SIEM Tour
In less than 10 minutes you can walk through the platform and get a deeper dive on the differentiated capabilities.

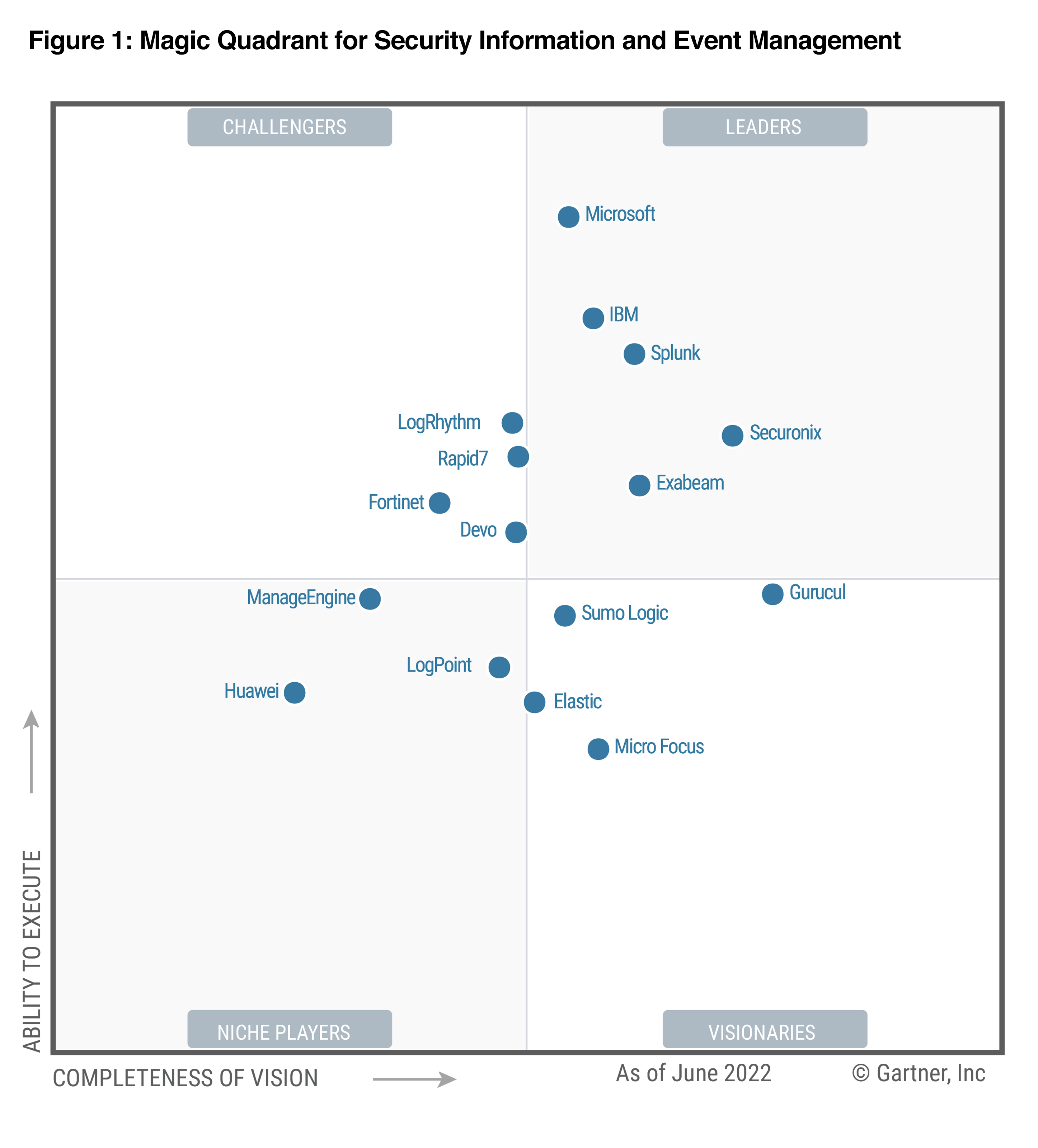
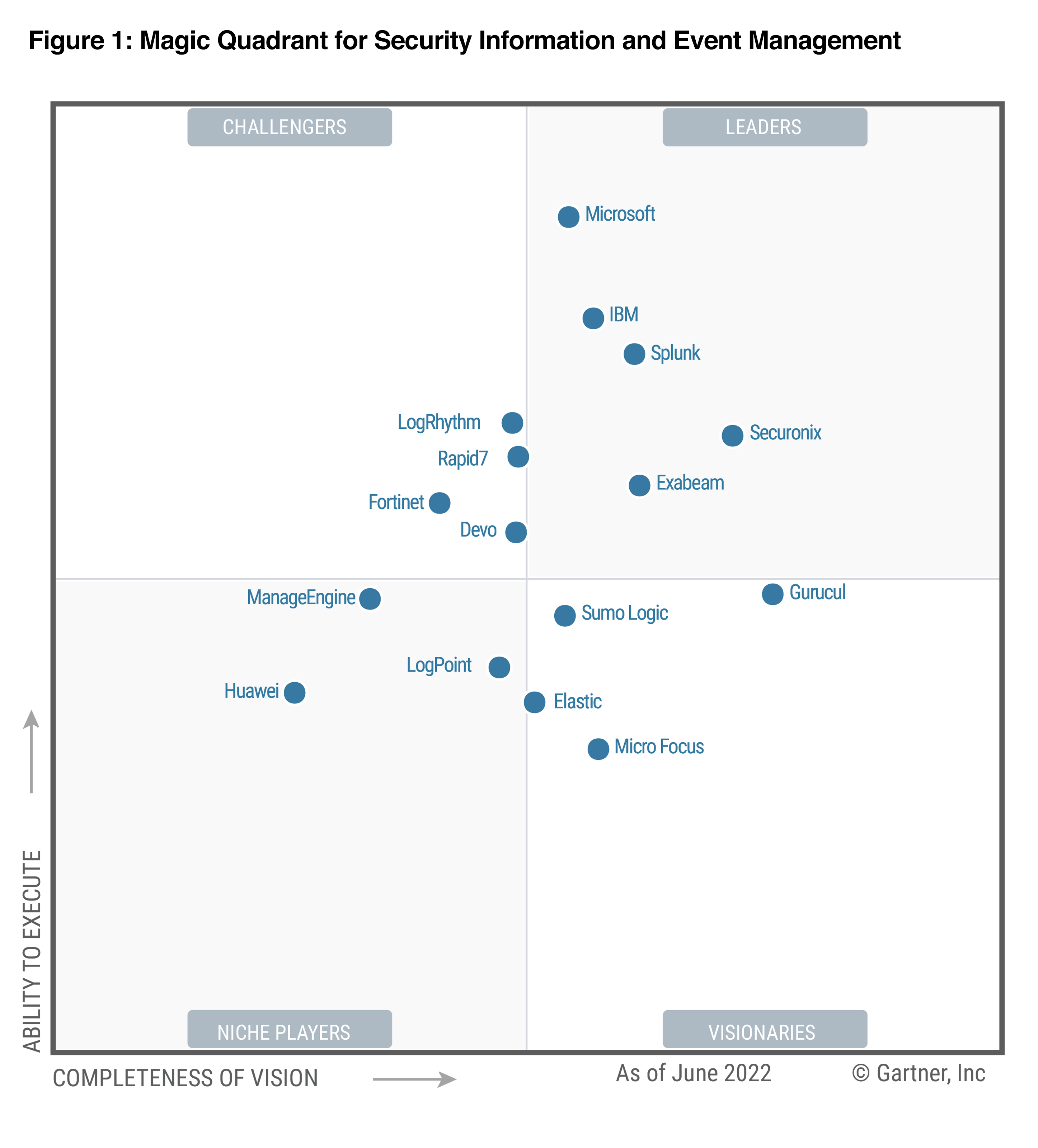
Most Visionary Platform in the SIEM Market
Gurucul was positioned furthest to the right for completeness of vision in the 2022 Gartner® Magic Quadrant™ for SIEM.
Gurucul ranked in the top 3 for all three SIEM use cases in the 2022 Gartner Critical Capabilities for SIEM.
Read Why Customers Recommend Gurucul
Build Your Next-Gen SIEM Business Case
Decrease mean time to detect and respond
Increase staff productivity with machine augmentation
Remove data store lock-in and avoid data transport costs
Gain predictability and freedom over data costs
Accelerate analyst training, efficacy and retention
NEXT-GEN SIEM
A Fully-Connected Security Stack
Gurucul’s Next-Gen SIEM platform has over 450 integrations, providing a single source for your security team to collaborate and boost productivity.
Start with SIEM Augmentation. End with SOC Transformation.
Explore Popular Next-Gen SIEM Use Cases
Use Case |
Current Challenge |
Gurucul Promise |
|---|---|---|
Monitor Complex Cloud Infrastructure and Detect Multi-Cloud Attack Campaigns |
Legacy SIEMs weren’t architected to support hyper-distributed multi-cloud environments, leading to gaps in threat detection, investigation and response, along with too many point solutions and complexity. | Our Next-Gen SIEM is cloud-native, open and architected to federate security analytics across all globally dispersed and heterogeneous environments and data stores. |
Prevent Insider Threats, Data Exfiltration, and Privileged Access Violations |
Legacy solutions are often too early in escalating risks, leading to false positives and manual case development; or they are too late, resulting in reactive recovery rather than proactive prevention. | The ability to discern context by cross-validating identity access, user behavioral and business application data makes our Next-Gen SIEM uniquely positioned to precisely identify real threats before exfiltration occurs. |
Detect Known and Unknown Threats in Real-time |
Legacy SIEM solutions lack visibility and their static rules-based models lack the ability to discern true threats. | Our Next-Gen SIEM rapidly ingests all relevant security data and uses the most robust ML threat models to detect real threats. |
Automate Threat Hunting with AI/ML |
Threat hunting with legacy SIEMs is cumbersome and time consuming, reserved for highly specialized and hard to find talent. | The 2,500+ trained and customizable ML threat models enriched by threat intelligence feeds empower all analysts to become effective threat hunters via the automation power of machine augmentation. |
Prove Compliance with Regulatory Mandates |
Lack of visibility, disparate security solutions, siloed data, manual processes, and departmental obfuscation make proving compliance painful and ineffective. | Our Next-Gen SIEM helps to facilitate compliance with standards and regulations such as ISO/IEC 27001, NIST 800-53, DFARS, ITAR, PCI DSS, HIPAA, the IoT Cybersecurity Act, and others. |
Legacy SIEM Wasn’t Built for This
Unleash the power of converged security analytics with Gurucul’s Next-Gen SIEM. Unearth real threats and augment your human security pro’s with machine intelligence.
FAQs
What’s the difference between SIEM and Next-Gen SIEM?
Next-Gen SIEM solutions are the necessary evolution of traditional SIEM solutions due to radical advancements in IT complexity and threats. Next-Gen SIEM solutions are more advanced, cloud-native security analytics solutions that offer a unified platform of converged capabilities spanning log management, UEBA, Identity & Access analytics, SOAR, Machine Learning, AI and threat intelligence.
What’s the difference between Next-Gen SIEM and XDR?
The lines are blurry and as Next-Gen SIEM platforms continue to offer more convergence it will be more difficult to understand the differences. XDR was a good response to SIEM solutions ineffectiveness, but introduces another problem of siloed analytics. Most Next-Gen SIEM platforms offer all of the capabilities available from XDR, but most XDR solutions lack critical capabilities of a Next-Gen SIEM.
Do I need to rip and replace my current SIEM?
Absolutely not. Next-Gen SIEM solutions can be introduced to augment the data source limitations, threat detection gaps and cost spikes you’re experiencing from legacy SIEM. Rip and replace is rarely a viable approach when dealing with such monolithic and entrenched technologies. Next-Gen SIEM use cases allow you to start small, think big and scale fast in-order to eventually phase-out or minimize your legacy SIEM footprint.
Is Next-Gen SIEM difficult to implement?
Nothing in cybersecurity is easy. However, best Next-Gen SIEM solutions offer immediate results upon deployment with out-of-the-box ML threat models that will give you immediate resultsI. Given the modern, cloud-native and open architecture of Next-Gen SIEM solutions you’ll benefit from easier and more inclusive interoperability with your IT and Security stack. Furthermore, the open architecture of the best Next-Gen SIEM solutions means flexibility in selecting the appropriate data to ingest from your choice of data lakes.
How does a Next-Gen SIEM work with my DLP?
Data Loss Prevention (DLP) is an important tool for security teams, often mentioned as a way to prevent users or threat actors from exfiltrating sensitive information via email, cloud storage services, and unauthorized file transfers. However, it is reactive and sometimes too late to stop data exfiltration. Next-Gen SIEM is an approach to security operations that enables organizations to aggregate DLP logs with information from all of their disparate devices to get a better picture of threats in the environment in order to detect and even predict when a user or threat actor is about to exfiltrate data before it becomes a breach.
How do I know if I need a Next-Gen SIEM?
If your current SIEM is struggling to keep up with sophisticated attacks, new security directives or use cases like Threat Detection Investigation and Response (TDIR) or if the costs are spiraling out of control, it might be time to augment your SIEM to solve for business critical use cases rather than accept blind spots in visibility or poor performance.

