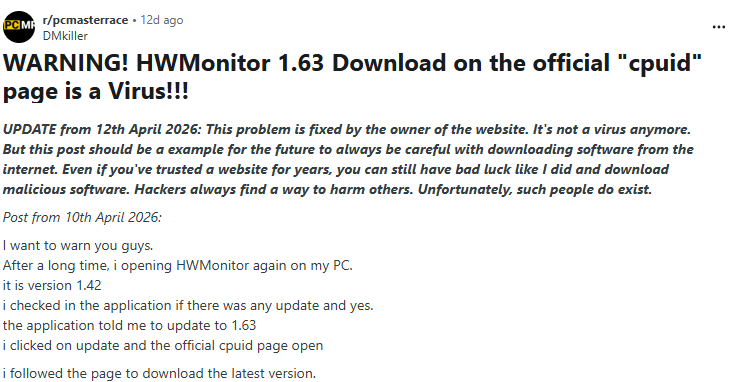
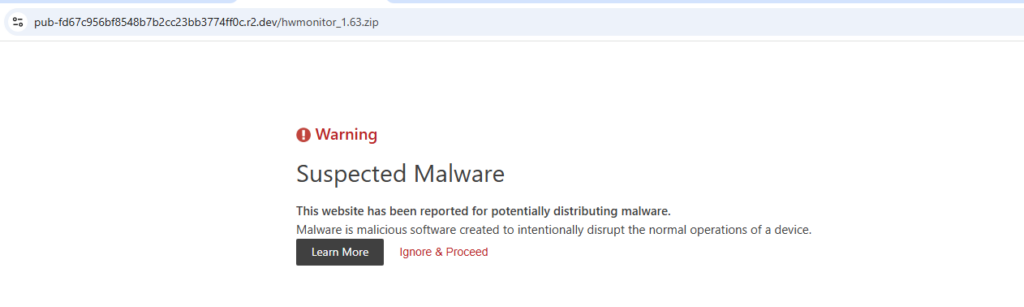
HWMonitor, a legitimate hardware monitoring utility developed by CPUID, was observed distributing a trojanized archive through a compromised download workflow. Analysis of a Reddit post led to the discovery of a malicious ZIP archive hosted on a Cloudflare R2 endpoint masquerading as a legitimate HWMonitor package.
The malicious archive was distributed through the following URL:
hxxp://pub-fd67c956bf8548b7b2cc23bb3774ff0c[.]r2[.]dev/hwmonitor_1[.]63[.]zip
This campaign demonstrates how attackers continue to abuse trusted software distribution channels to deliver malware through DLL sideloading and memory-resident execution chains. Because users generally trust widely used software utilities, trojanized installers remain an effective initial access vector.
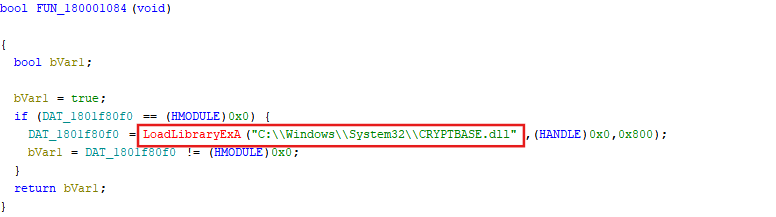
Following extraction, the archive contains a suspicious CRYPTBASE.dll colocated with the legitimate HWMonitor_x64.exe binary.
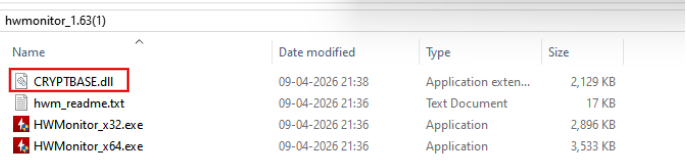
The malware abuses DLL search-order hijacking by placing a malicious DLL within the application directory, causing the executable to load the attacker-controlled library instead of the legitimate Windows system DLL.
Upon execution, the malicious DLL initiates a multi-stage in-memory loading chain that ultimately deploys STX RAT. The malware employs several defense evasion and stealth techniques, including:
The final payload includes functionality associated with credential theft and remote operator interaction through hidden desktop monitoring behavior.
In this campaign, HWMonitor_x64.exe loads CRYPTBASE.dll from the local application directory instead of the legitimate Windows system path, allowing attacker-controlled code to execute within the trusted process context.
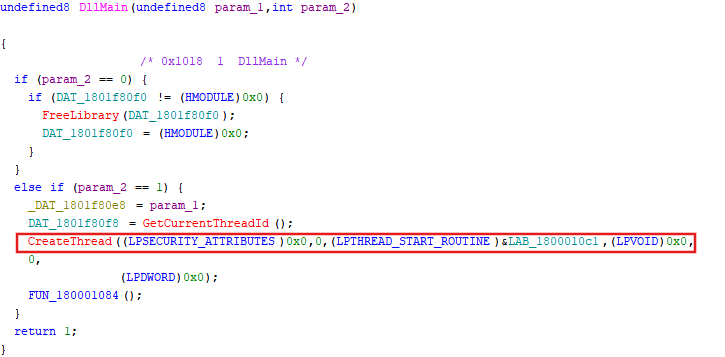
After execution, the malicious DLL loads the legitimate cryptbase.dll from the Windows system directory to preserve normal application functionality and reduce user suspicion.

Inside DllMain, the malware spawns two separate threads:
Launching the malicious logic through a secondary thread likely avoids loader-lock-related instability commonly associated with executing complex logic directly from DllMain.
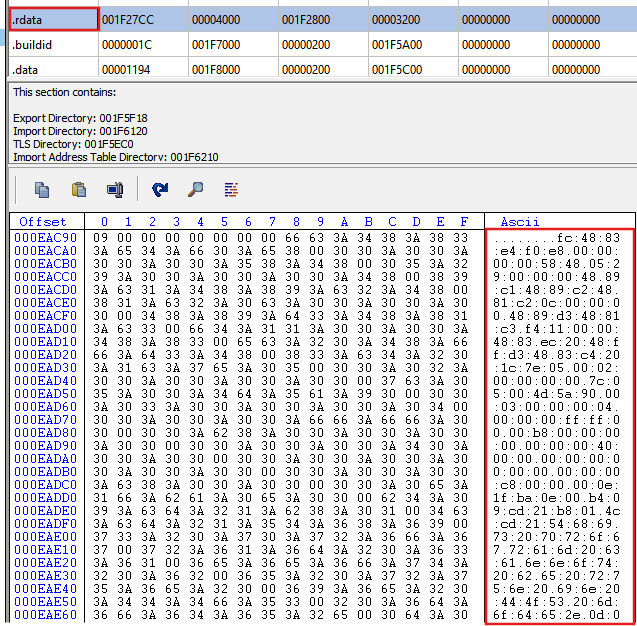
The malicious DLL extracts obfuscated data from the .rdata section and allocates executable memory using VirtualAlloc with RWX permissions. The allocated memory region is populated with decoded shellcode and an embedded PE payload.
Execution is then transferred to shellcode responsible for reflective PE loading. The loader manually maps embedded payloads entirely in memory by:
This staged architecture allows the malware to avoid writing intermediate payloads to disk, significantly reducing forensic artifacts.

The malware proceeds through multiple reflective loading stages, where each stage decrypts and loads the next payload directly in memory using a TEA-like symmetric decryption routine.
The overall execution chain observed during analysis is shown below:
| HWMonitor_x64.exe └── Malicious CRYPTBASE.dll └── Stage 1 Shellcode Loader └── Reflective Stage 2 Loader └── Stage 3 Intermediate Loader └── Stage 4 Final Loader └── STX RAT Payload |
Stage 2 and Stage 3 operate as intermediate reflective loaders responsible for decrypting and mapping the next payload stage entirely in memory.
Stage 4 follows the same execution pattern and ultimately decrypts and loads the final STX RAT payload without writing artifacts to disk.


STX RAT dynamically resolves APIs using a ROR13 hashing routine combined with PEB traversal, eliminating explicit import table dependencies and complicating static analysis.
The malware enumerates loaded modules through the PEB loader structures and parses export tables to resolve functions by comparing runtime-generated hashes against hardcoded constants embedded within the binary.
This technique enables the malware to conceal sensitive API usage while maintaining flexible runtime resolution.

The malware implements a lightweight anti-debugging mechanism by directly accessing the Process Environment Block (PEB) and inspecting the BeingDebugged flag located at offset 0x2.
By avoiding standard debugging detection APIs, this approach reduces behavioral visibility while allowing the malware to alter execution flow when analysis tools are detected.

STX RAT enumerates installed security products, including antivirus and EDR solutions such as:
The product names are stored using a lightweight XOR-based obfuscation routine in which each byte is XORed using an incrementing key beginning as 0x36.
This obfuscation technique reduces static signature visibility while remaining computationally inexpensive.
Security software discovery may allow operators to profile the victim environment and adapt post-compromise behavior based on defensive tooling present on the system.

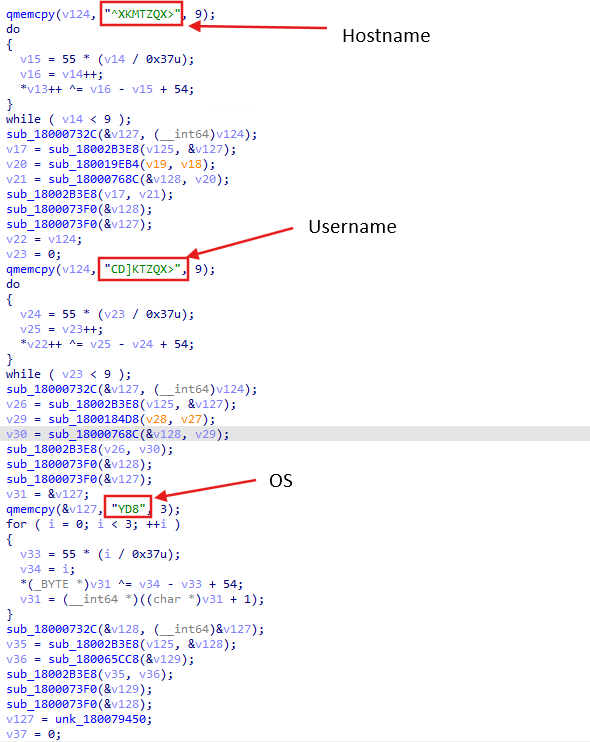
The malware collects basic host profiling information including:
Collected values are obfuscated using the same XOR-based routine observed elsewhere in the malware.
This information enables victim tracking, infection management, and campaign-level host identification.
STX RAT interacts with the interactive window station (WinSta0) using OpenWindowStationW, requesting permissions associated with desktop creation and screen interaction.

The malware subsequently enumerates windows through Z-order traversal using GetWindow, selectively processing visible windows that may contain sensitive user activity.

Screen content is captured using BitBlt with the SRCCOPY raster operation (0xCC0020), enabling lossless capture of visible desktop content.
Combined, these behaviors are consistent with hidden-desktop-based monitoring capabilities commonly associated with HVNC-style malware frameworks.
Captured content could facilitate theft of browser-displayed credentials, authenticated sessions, and other sensitive user activity.

The malware constructs structured JSON-based network data used for command-and-control communication.
Observed configuration fields include:
| Field | Description |
tag | Campaign identifier |
referrer | Infection source identifier |
callback | Remote registration endpoint |
The presence of campaign tracking identifiers suggests the operators may distribute multiple trojanized software packages while tracking infection sources independently.

Observed callback endpoint:
hxxps://welcome.supp0v3[.]com/d/callback
Gurucul SIEM can help security teams detect and investigate activity associated with this malware campaign by providing visibility into:
By correlating endpoint, process, memory, and network telemetry, Gurucul can assist SOC teams in identifying stealthy multi-stage malware activity and improving detection coverage for memory-resident threats.
| Tactic | Technique ID | Technique Name | Observed Activity |
| Initial Access | T1195 | Supply Chain Compromise | Compromised HWMonitor download page distributing malicious ZIP via Cloudflare R2 |
| Execution | T1574.001 | DLL Side-Loading | Malicious CRYPTBASE.dll loaded by HWMonitor instead of legitimate system DLL |
| Execution | T1055 | Reflective Loading | Reflective DLL loading and in-memory execution of subsequent stages |
| Defense Evasion | T1027 | Obfuscated/Encrypted File or Information | XOR-based string obfuscation and TEA encryption for payload stages |
| Defense Evasion | T1622 | Debugger Evasion | PEB BeingDebugged flag check (+2 offset) |
| Discovery | T1082 | System Information Discovery | Collection of hostname, username, and OS details |
| Discovery | T1518 | Software Discovery | Identification of installed AV/EDR solutions |
| Collection | T1113 | Screen Capture | Use of BitBlt (0xCC0020) for capturing screen |
| Collection | T1056 | Input Capture | Capturing browser sessions and user input via screen monitoring |
| Command and Control | T1071.001 | Web Protocols | JSON-based communication with C2 over HTTP/HTTPS |
| Command and Control | T1105 | Ingress Tool Transfer | Downloading additional payload stages from remote server |
| Command and Control | T1573 | Encrypted Channel | Obfuscated communication using structured JSON and encoded data |
| Defense Evasion | T1218 | Signed Binary Proxy Execution | Abuse of legitimate HWMonitor binary to execute malicious DLL |
| File | MD5 |
| hwmonitor_1.63_malware.zip | f19f331562052baea0114d5186bbffd4 |
| CRYPTBASE.dll | ab122aa36bfebf4f249c4eb617e4a6cb |
| Stage 2 Loader | D3C186869F443B6C1BE127A59B0B5A89 |
| Stage 3 Loader | ADAB6C337E403AF0040D77A56DAF3BA0 |
| Stage 4 Loader | 9BF17E6525A295FB6E5EB562DEB927AE |
| STX RAT Payload | C781B1B559A585BB764B10176D64486C |
| Type | Indicator |
| Callback URL | hxxps://welcome.supp0v3[.]com/d/callback |
| Malware Distribution URL | hxxp://pub-fd67c956bf8548b7b2cc23bb3774ff0c[.]r2[.]dev/hwmonitor_1[.]63[.]zip |
Contributors:
Pandurang Terkar

Rudra Pratap

