By collecting and analyzing data from across an organization’s entire computing environment, a SIEM enables security teams to identify and respond to security events in real-time.
SIEM (pronounced “sim”) stands for Security Information and Event Management. It is a type of software solution that provides security professionals with a centralized view of their organization’s security events, including alerts, incidents, and logs.
SIEM systems collect and analyze security-related data from multiple sources, including network devices, servers, endpoints, cloud platforms, applications, and more. They then use advanced analytics and correlation techniques to identify potential security threats, anomalies, and patterns that could indicate a security breach or attack.
SIEM solutions also can provide real-time alerts, automated response actions, and reporting capabilities that help organizations detect, investigate, and respond to security incidents more efficiently and effectively. Another key function is to provide reporting to support industry and regulatory compliance requirements.
SIEM solutions have been around for at least a decade. The original solutions, now known as “legacy SIEM,” have become obsolete due to advances in technology and changes in security threats. These older SIEM solutions were typically installed on-premises and had limited scalability, making it difficult for them to keep up with the evolving security landscape and the increasing volume of security data generated by modern networks. Legacy SIEMs also require more manual intervention and customization, which can be time-consuming and costly. Organizations that still rely on legacy SIEM systems are at risk of missing critical security events, failing to detect advanced threats, and experiencing security breaches.
Today’s SIEM solutions are often referred to as “Next-Gen SIEM,” meaning the solution has the next generation of advanced features and capabilities, such as machine learning, artificial intelligence, big data storage, behavior analytics, and cloud integration. These technologies combine to provide more effective threat detection, response, and automation capabilities. Next-Gen SIEM solutions are designed to overcome the limitations of legacy solutions and address the evolving threat landscape and the increasing volume and complexity of security data generated by modern networks and cloud computing.
Many Next-Gen SIEM vendors offer a cloud-native SIEM solution. That is, the SIEM is specifically developed to run on a cloud platform and is able to take advantage of cloud architectures and features, such as scalability and frequent software updates.
Next-Gen SIEM solutions offer several key benefits, including:
Advanced Threat Detection – Machine learning and behavioral analytics are used to identify and prioritize threats that legacy SIEM systems might miss. This enables security teams to detect and respond to threats – including unknown threats – faster and more efficiently.
Automation and Orchestration – Many security tasks, such as incident response, triage, and remediation, are automated, which frees up security teams to focus on more critical security issues. Next-Gen SIEM solutions can integrate with other security solutions (such as SOAR) to provide a more comprehensive security ecosystem.
Cloud-Enabled – Next-Gen SIEM solutions can work in cloud, hybrid, or on-premises environments, enabling organizations to manage their security data from anywhere, anytime.
Scalability and Flexibility – Next-Gen SIEM solutions can scale to accommodate large and diverse security data sets and are flexible enough to adapt to changing security needs and requirements.
A SIEM is considered to be an enterprise platform because it has purview over an organization’s entire computing platform. The system collects data from as many sources as possible – the more, the better – and standardizes the data so that it can be correlated and analyzed for threats. Once a potential threat is surfaced, the system may gather additional contextual information and send an alert so that a security analyst can initiate an investigation if warranted. The system may also generate an automated response to a common threat, if desired. The system generates reports that track the threats and provide information for audit purposes.
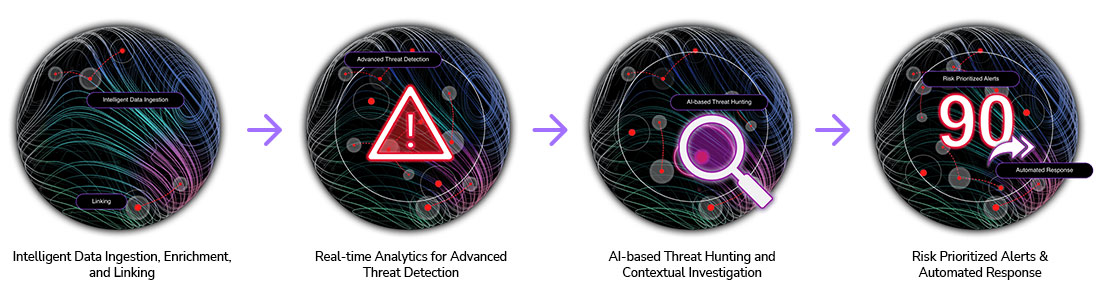
The process of a SIEM typically involves the following steps:
Data collection – Security-related data is collected from various sources, such as servers, network devices, security appliances, cloud platforms, applications, and security solutions like firewalls, IDS/IPS, and antivirus. This data can include log files, network traffic, system events, and more.
Data normalization – The collected data is normalized, which means it is put into a standardized format so that it can be easily processed and analyzed.
Data correlation – The collected data is correlated to identify relationships and patterns that may indicate a security threat or attack. This involves combining data from multiple sources and identifying events that may be related to each other.
Alert generation – If the SIEM system detects a security threat or attack, it generates an alert, which is typically sent to a security analyst or team for further investigation.
Incident investigation – The security analyst or team investigates the alert generated by the SIEM system to determine the nature and severity of the threat or attack. This may involve analyzing additional data, such as system logs, network traffic, and other security-related events.
Incident response – Once the nature and severity of the threat or attack are determined, the security team takes action to contain, mitigate, and resolve the incident. This may involve taking steps to stop the attack, restore systems and data, and prevent similar attacks from happening in the future.
Reporting and analysis – The SIEM system provides reporting and analysis capabilities that allow security teams to track security events, identify trends and patterns, and measure the effectiveness of their security measures. This information can be used to improve security policies, procedures, and technologies, and to help prevent future security incidents.
Overall, the SIEM process is an iterative process that involves continuous monitoring, analysis, and improvement to ensure that an organization’s security posture is maintained and even enhanced.
Computing environments have grown very complex, now extending from the user workstation, to the on-premises datacenter, to the cloud. At the same time, cyberattacks have grown more prevalent and more sophisticated. Monitoring the enterprise environment for threats and detecting them before harm can be done has grown far beyond the capacity of what humans can do manually. Thus, there is a need to automate the process of collecting security information and analyzing it for threats. The right SIEM solution is able to filter through all the data and prioritize threat alerts, making security more manageable.
Three of the main reasons organizations need a SIEM solution include:
Detecting Incidents – A SIEM solution detects incidents that otherwise can go unnoticed. This technology analyzes log entries and other relevant security events from across the enterprise to detect indicators of threats in the environment. Moreover, since it gathers events from all sources across the network, the system can reconstruct the attack’s timeline and path to help determine its nature and impact. The platform communicates its findings to the security team for further investigation.
Incident Management – A SIEM improves incident management by allowing the security team to identify an attack’s route across the network, identifying the compromised sources and providing automated mechanisms to stop the attack in progress.
Compliance with Regulations – Companies use a SIEM to meet compliance requirements by generating reports that address all logged security events among these sources. Without a SIEM, an organization needs to manually retrieve log data and compile the reports.
The SIEM process involves collecting security-related data from various sources, analyzing the data to detect security incidents, and providing actionable insights to security teams to help them respond to threats. Here is the general flow of how a SIEM solution works.
Data Collection – The first step in the process is to collect data from various sources such as network devices, servers, endpoints, and security solutions like firewalls, IDS/IPS, and antivirus. This data can include logs, network flows, user and system activity, and security events.
Data Parsing and Normalization – Once the data is collected, it is parsed and normalized to ensure that all data is in a consistent format that can be easily analyzed. This is done by mapping different log formats to a standard format, so that they can be analyzed together.
Data Storage and Indexing – The normalized data is then stored in a central repository, where it can be easily accessed and analyzed. The data is indexed, so that it can be searched and queried quickly.
Event Correlation and Analysis – The SIEM tool analyzes the collected data for patterns and correlations to identify potential security incidents. This involves correlating events from different sources and identifying anomalies that may indicate a security threat.
Alert Generation – Once a security incident is detected, the SIEM tool generates alerts to notify security teams. These alerts can be in the form of email, SMS, or other notifications.
Incident Response – The security team investigates the alerts generated by the SIEM tool to determine the severity of the threat and the appropriate response. This may involve blocking traffic, isolating affected systems, or escalating the incident to higher-level security teams.
Reporting and Visualization – SIEM tools provide reports and dashboards that enable security teams to view and analyze security events and incidents. These reports can provide insights into security trends, compliance violations, and other security-related issues.
Continuous Improvement – The SIEM process is an iterative process that involves continuous monitoring, analysis, and improvement. Security teams can use the insights gained from the SIEM tool to improve their security posture and reduce the risk of security incidents.
The most important features and functions of a SIEM tool are data collection, real-time event correlation, alerting and notification, incident management, reporting and dashboards, threat intelligence, compliance management, and scalability.
Data Collection, Normalization and Storage – The SIEM tool should be able to collect data from a wide range of sources across an organization’s entire computing environment, for example, logs, network flows, user and system activity, and security events. The tool should be able to map the collected data to a standard format to ensure that different types of log data can be analyzed together. All the data should be stored in a central repository for ready availability.
Threat Intelligence – The SIEM tool should be able to integrate with third-party threat intelligence feeds in order to provide additional context and insights into security events and incidents.
Real-time Event Correlation and Analysis – The SIEM tool should be able to analyze security-related events in real-time and correlate events from different sources to identify potential security incidents. SIEM solutions vary greatly in their level of data analysis. Solutions that incorporate next-gen technology such as machine learning, artificial intelligence, and behavior analytics help to investigate more sophisticated and complex attacks as they arise, including insider attacks.
Alerting and Notification – The SIEM tool should be able to generate alerts and notifications when security incidents are detected. These alerts should be customizable and prioritized, and should be able to be sent via email, SMS, or other notification channels.
Incident Management – The SIEM tool should have a built-in incident management system that enables security teams to investigate and respond to security incidents. The system should enable teams to track incidents from detection to resolution.
Reporting and Dashboards – The SIEM tool should provide a range of out-of-the-box reports and dashboards that enable security teams to view and analyze security events and incidents. The reports should be customizable and should enable teams to drill down into the data to identify trends and anomalies.
Compliance Management – Regulatory compliance requirements can vary considerably from one organization to the next. The SIEM tool should be able to assist with compliance management by providing reports and dashboards that enable teams to demonstrate compliance with their specific regulatory requirements.
Scalability and Flexibility – The SIEM tool should be able to scale to meet the needs of large organizations with multiple data sources and a high volume of security events. It should offer the flexibility to be installed on premise, if required, or run in the cloud.
Integrations – The SIEM should be able to integrate with an organization’s existing security tools as well as with non-security log sources. This will help improve coverage and preserve the organization’s return on investment in existing tools.
A SIEM solution provides both technical and business benefits. Here are some of the main benefits:
Improved Security Visibility – A SIEM solution provides a centralized view of security events and incidents across an organization’s entire IT infrastructure. This enables security teams to detect and respond to security threats in real-time, including those that might otherwise go unnoticed, which improves overall security posture.
Improved Incident Detection and Response – With a SIEM solution in place, security teams can quickly detect and respond to security incidents before they become major breaches. The real-time event correlation and alerting capabilities of a SIEM solution help security teams respond to incidents in a timely manner. This can help to minimize the impact of security incidents and reduce the time and resources required to resolve them.
Improved Threat Intelligence – A SIEM solution can integrate with external threat intelligence feeds to provide additional context and insights into security events and incidents. This can help organizations stay ahead of emerging threats and proactively defend against them.
Reduced Downtime and Business Impact – By quickly detecting and enabling a response to security incidents, a SIEM solution can help reduce downtime and minimize the impact on business operations. This can save organizations time and money and help maintain customer trust.
Compliance Management – SIEM tools help organizations to comply with regulatory requirements by providing the ability to monitor and report on security-related activities. Also, by providing reports and dashboards that demonstrate compliance with regulatory requirements, SIEM tools can help organizations avoid fines and penalties.
Operational Efficiency – SIEM tools enable organizations to centrally manage their security operations, making it easier to monitor and respond to security incidents across the organization. Moreover, by automating security event collection, normalization, and analysis, a SIEM solution can help reduce the workload on security teams and enable them to focus on higher-value activities such as incident response and threat hunting.
Cost Savings – By detecting and responding to security incidents quickly, SIEM tools can help organizations to minimize the impact of security incidents and reduce the costs associated with incident response.
User and Entity Behavior Analytics (UEBA) is a type of technology that is sometimes used in SIEM systems. UEBA focuses on analyzing the behavior of end users and entities (such as servers, applications, and network or IoT devices) to detect anomalous or suspicious activities that may indicate a security threat.
UEBA systems typically use machine learning and data analytics to establish a baseline of normal behavior for each user and entity, and then monitor for deviations from that baseline. This can help security teams identify potential insider threats, compromised accounts, and other security incidents that might otherwise go unnoticed.
By integrating UEBA with SIEM, security teams can gain greater visibility into their organization’s security posture and respond more quickly to potential threats. Now that you can answer the question, “What is UEBA in SIEM?” let’s learn more about SIEM and SOAR.
Security Orchestration, Automation, and Response (SOAR) is a technology that complements SIEM by providing a more automated and streamlined approach to incident response.
SIEM systems are designed to collect and analyze security events from across an organization’s network and systems. They help security teams detect and investigate potential security incidents, but they can generate a large volume of alerts and require a significant amount of manual effort to manage.
SOAR technology, on the other hand, provides a way to automate and orchestrate the response to security incidents detected by the SIEM system. It enables security teams to create automated workflows that can help to quickly triage and respond to alerts, reducing the time required to investigate and remediate security incidents.
By integrating SOAR with SIEM, security teams can:
Reduce response times – SOAR can automate the initial stages of incident response, such as gathering information and performing initial triage, allowing security teams to respond more quickly to potential threats.
Improve efficiency – By automating repetitive tasks, SOAR can free up security analysts to focus on more complex and critical tasks.
Enhance accuracy – SOAR can help to standardize incident response processes, reducing the risk of errors and improving the consistency of response across different incidents.
Increase visibility – SOAR can provide real-time visibility into incident response workflows, helping security teams identify bottlenecks and areas for improvement.
In short, the combination of SIEM and SOAR can help organizations to improve their security posture by reducing the time and effort required to detect, investigate, and respond to security incidents.
Gurucul Next-Gen SIEM is a cloud-native, modular platform for consolidating core Security Operations Center (SOC) solutions into a single pane of glass aligned with the evolving needs of the modern enterprise threat landscape. The product quickly identifies and addresses new, emerging, and unknown threats that evade rule-based machine learning solutions, while improving security operations through greater data ingestion, reduced threat detection time, automation of manual processes, and improved analyst efficiency.
Through our innovative approach, Gurucul improves and simplifies the security analyst experience even as we provide greater context, automation of manual tasks, and risk-driven prioritization of response actions. While driving efficiencies across security operations, these unique capabilities have been proven to drastically reduce total cost of ownership (TCO):
Don’t just take our word for it. For several years, Gurucul has been positioned furthest to the right for completeness of vision in the Gartner® Magic Quadrant™ for SIEM. Gartner’s evaluation is based on specific criteria that analyzed the company’s overall completeness of vision and ability to execute.
Discover what Gartner has to say about how Gurucul is positioned in the SIEM Market.
As cyberattacks grow more pervasive and computing environments more complex, security teams need the proper tools to detect and respond to threats. Next-generation SIEM solutions provide a more efficient and effective way to monitor and manage security events, enabling organizations to take action to address threats quickly and accurately while reducing the burden on security teams.
Organizations that utilize a SIEM solution enjoy the benefits of improved security visibility, faster incident detection and response, reduced downtime and business impact, compliance management, operational efficiency, and improved threat intelligence.
About The Author
 Jane Grafton, VP Marketing, Gurucul
Jane Grafton, VP Marketing, Gurucul
Jane Grafton has more than 30 years of experience in domestic and international marketing, sales and business development. She came to Gurucul from Lieberman Software where she spent 9 years managing global marketing operations inclusive of marketing automation, website, events, collateral, digital marketing, email campaigns, product marketing, PR and corporate branding. Prior to that she spent 12 years at Sun Microsystems in field marketing management, supporting commercial accounts and federal systems integrators throughout the U.S. Prior to Sun, Mrs. Grafton sold and developed new markets for Locus Computing Corporation’s UNIX software services focusing on OEMs. At Computer Associates Limited in the UK, she established a new corporate function, Third Party Marketing, by developing relationships with hardware manufacturers, distributors and management consultants. Mrs. Grafton graduated from UC San Diego, CA in Applied Mathematics.
Security Information Management (SIM), Security Event Management (SEM), and SIEM are all security management solutions that collect and analyze security data from multiple sources to detect and respond to security incidents. However, there are some key differences.
SIM solutions focus on collecting and analyzing security event data, such as logs and alerts, from various security technologies, including firewalls, intrusion detection and prevention systems (IDS/IPS), and anti-virus/anti-malware solutions. SIM provides a centralized view of an organization’s security posture.
SEM focuses on the real-time monitoring and analysis of security events, with a primary focus on the detection of and response to security incidents.
SEM solutions typically collect and analyze data from various security technologies and generate alerts when security events or anomalies are detected.
In short, SIM systems are designed to provide a broad view of an organization’s security posture, while SEM systems are designed to provide a more focused, real-time view of potential security incidents.
Relative to both SIM and SEM, SIEM solutions provide a broader and more comprehensive approach to managing security information and events. SIEM solutions not only collect and analyze security event data but also store and correlate the data to identify patterns, trends, and threats across multiple sources. This enables security teams to identify potential threats and vulnerabilities proactively, rather than just reacting to security events as they occur.
SIEM solutions also provide advanced analytics capabilities, such as machine learning, behavior analytics, and threat intelligence, to identify and prioritize potential security threats. SIEM solutions often provide more extensive compliance and reporting capabilities, enabling organizations to meet regulatory requirements and industry standards.
SIEM tools are designed to provide organizations with greater visibility into their security posture, enabling them to detect and respond to potential threats more quickly and effectively. This is accomplished through a number of key functions, including log collection, log analysis, event correlation, threat detection, incident response, and compliance reporting.
A SIEM system collects and analyzes security-related data from multiple sources, including network devices, servers, endpoints, cloud platforms, and applications. It uses advanced analytics and correlation techniques to identify potential security threats, anomalies, and patterns that could indicate a security breach or attack.
SIEM also can provide real-time alerts, automated response actions, and reporting capabilities that help organizations detect, investigate, and respond to security incidents more efficiently and effectively. Another key function is to provide reporting to support industry and regulatory compliance requirements.
A Security Operations Center (SOC) is a centralized facility that is responsible for monitoring, detecting, and responding to potential security incidents across an organization’s network and systems. The SOC is staffed by security analysts who use a range of technologies, including SIEM tools, to collect and analyze security event data from across the organization.
The SOC is responsible for identifying potential security incidents, investigating and triaging those incidents, and coordinating the response to those incidents. The ultimate goal of the SOC is to detect and respond to security incidents quickly and effectively, in order to minimize the impact of those incidents on the organization’s operations and assets.
Gurucul Next-Gen SIEM is one of the leading examples of a Security Information and Event Management systems on the market. In fact, Gurucul has been positioned ahead of all competitors for completeness of vision in the Gartner® Magic Quadrant™ for SIEM.
